How Scammers Use AI For Phishing
Scammers are using AI to create phishing messages that are more convincing,...
Password Manager Security Risks and Breaches
Password managers are generally safer than reusing passwords, but they do create...
Why you need to reboot your router regularly to fix security issues
Rebooting a router can help because many router infections and bad connections...
FCC Has Banned Import of Consumer-grade Routers Amid National Security Concerns
Federal regulators have moved to cut off a major supply line into...
Meta’s New Anti-Scam Tools Now on WhatsApp, Facebook and Messenger
Meta is rolling out new AI‑powered defenses against online fraud, launching anti‑scam...
Multifactor Authentication / 2 Step Verification
Multifactor authentication (MFA) is a login security method that requires two or...
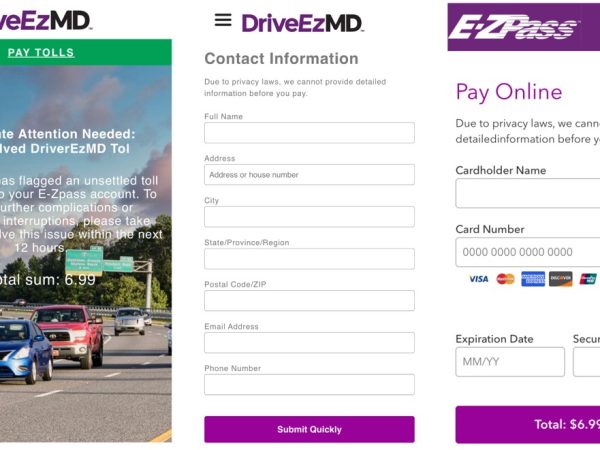
Scammers Are Cloning Official Government Websites
Scammers are cloning official government websites, including the FBI’s own cybercrime portal,...
Robocall Scam Targeting Walmart Shoppers
A widespread robocall scam is targeting Walmart shoppers — using fake AI...
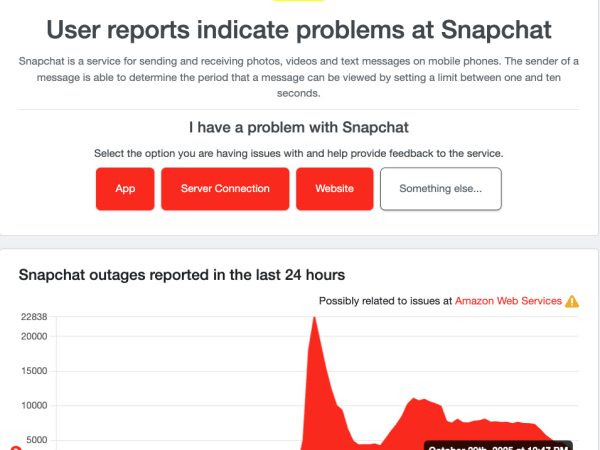
Amazon Web Services (AWS) Outage Breakdown: How One Cloud Glitch Disrupted the Web
On October 20, 2025, AWS experienced a major outage centered in its...
Microsoft Teams Launches Automatic Alerts for Malicious Links
Microsoft is rolling out a new security feature, Malicious URL Protection in...